Leveling Up Your Cyber Skills – A Guide To Capture The Flag (Part 3)
Hosting a CTF, Part 3: Tips To Create Meaningful Content For Jeopardy-Style CTF Events
Now that you have an idea of which categories you want, how do you actually create content?
Well, the first question is this: do you want to create challenges where you hide a specific flag (like flag:YouFoundMe or pyber{NetworksRFun}), or do you want to just create content that participant answer questions on (like “What’s the first domain name resolved in the provided .pcap file?”)?
If you want to create questions with specific flags in them, I recommend choosing a clear flag format and sticking with it so that you don’t confuse people. Having people find a random English word as the flag in a file can be rough because other English words that you didn’t think of maybe in the file and thus serve to confuse participants.
We typically go with the simple but effective “flag:ABCDEFG”. Another common format is “CTFNAME{something}”, likely to help make it clear when others simply steal their content and use it in another CTF. Whichever you choose, the main thing is that you should be consistent. We’ve had CTFs where some flags are “flag:ABCDEF”, some are “pcyber{ABCDEF}”, and another that was just text pasted into an image. Participants were confused: do they enter “flag:ABCDEF” this time or just “ABCDEF”? Is “Beef4Me” really the flag, or should I be looking for “flag:Beef4Me”?
I also highly recommend that you ensure that your questions aren’t all frustrating or require an “ah-ha” moment to solve (unless you really want this). Unless the participant thinks exactly like the author of the question, questions like “find the flag in this file” may be very hard or practically impossible to answer. For example, if you’re going to be clever and hide a flag in the urgent pointer field of the TCP header in successive packets in a .pcap, you may frustrate folks who analyze every packet in the .pcap for minutes and hours and not notice that oddity in the packet. If they notice nonzeros in the urgent point field of the .pcap, then it may be quick and easy for them to convert that to a human-readable flag, but if they don’t have that “ah-ha” moment of the oddity of the urgent pointer being set (something that’s not often seen in traffic), they may get frustrated. Writing good questions requires a balancing act though.
There are people that enjoy the challenge of finding the needle in the haystack. You can also try to better balance things by providing hints (each of which may reduce the maximum points that solving the question gets a participant, or may cost a participant points outright) that help guide a person to the flag so that they don’t get stuck. For the urgent pointer bit, you may have hints like “Look for a flag value set that’s not normally set in this type of traffic,” followed by “Focus on TCP flags,” after which you offer “Do you see anything odd sitting in any pointer fields?” and finally perhaps you give a humongous hint like “The flag is hidden in the urgent pointer field of several packets.”
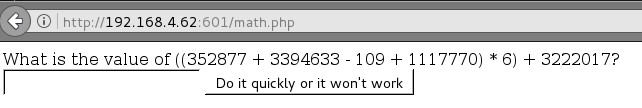
In my opinion, the best questions are those where the ultimate solution/goal is clear but where it takes work to get to that solution/goal. For example, we once had a web-coding question (see the image for what it looked like) where a webpage displayed a random, semi-complex math problem for which the answer to it had to be submitted within 2 seconds for the page to display the flag. You couldn’t do the math problem manually and submit the flag within the time period, so you had to write code to download the page, solve the problem, submit the answer, and show you the flag. Thus it was pretty clear from the start what needed to be done, but participants still had to figure out how to do it.
Challenges that answer a specific question about the content, rather than having to find a flag, tend to inherently have a clearer goal—and thus are less about finding a needle in a haystack.
For example, if you have a set of Bro/Zeek logs, you could ask the following: “What is the total number of packets seen in this log? You can determine this by totaling the number of all log lines containing ‘Bro interface pkts’.”
In the next post, we’ll go through some examples of creating your own content.
Check out our previous Cyber blogs: A Guide To Capture The Flag (Part 1)| A Guide To Capture The Flag (Part 2)